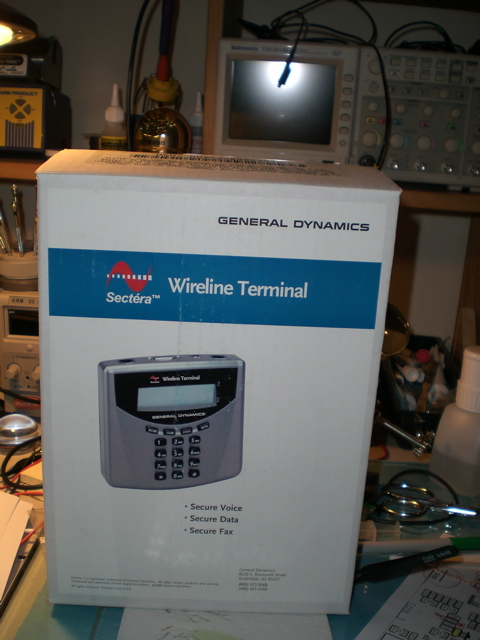
At a previous employer we evaluated a few of these devices so that executives could make "secure" calls form their homes to the office, but we ended up instead deploying an VoIP over IPSec solution. I ended up with these after the eval and always thought that they were cool, but never did anything with them.
Their marketing literature is filled with all sorts of exciting phrases like:
The Sectéra Wireline Terminal is NSA certified to protect information classified Top Secret and below using Type 1 encryption algorithms.
For users not requiring Type 1 encryption, an interoperable AES solution is available. The terminal is available with multiple key-sets to
support U.S. government sponsored interoperability (e.g., NATO and coalition).
When I was looking for something with a largish FPGA that I could re-purpose for password cracking I suddenly thought of these again and figured that they probably used an FPGA for the encryption bit, so I decided to open one up and have a look. I assumed that they probably had some sort of cool tricks built in so that opening the case would trip some sort of tamper switch and the device would instantly zero its keystore, or do something else to makes the device inoperable. Seeing as I didn't really think I'd use if as a voice encryption device anyway and was about to break the warantee sticker I decided to see if I could defeat the tamper switch, so I plugged the device in, generated a new public / private key pair and then very carefully drilled a hole through the back of the case. After much poking around with a probe, careful peering with a fiber scope, etc I decided to just risk it and undo the screws... Turns out that hte devices don't have any sort of tamper prevention, and it carried on running just fine, with no loss of keying material, etc.

The only security for the keystore seems to be the odd mounting bits that the FPGA sits on, but it seems that:
- that can be easily bypassed
- there is enough space to install additional circuitry to copy the date stream before encryption and transmit it later
- the flash is accessible to reprogram it and get it to expose the session keys somehow during call setup
- all of the FPGA pins are nicely broken out and can be probed with a logic analyzer.
I intend trying all of the above sometime, but ran out of time. For now here is a picture of the inside of the device with the FPGA visible.
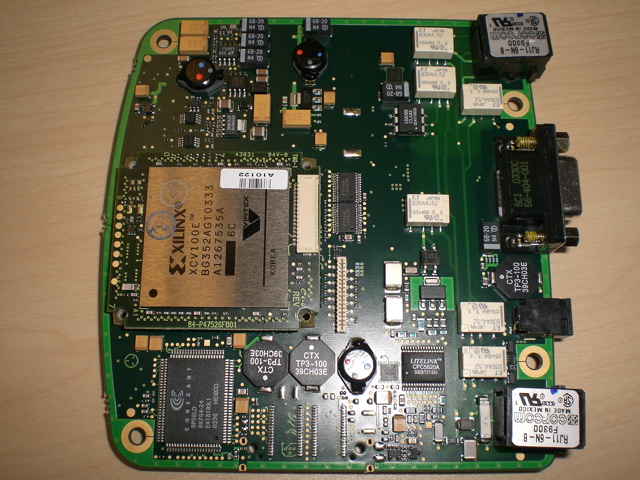
Link to Xilinx data sheet -- its got 128k gates and 81k of block RAM -- about perfect to be converted into an MD5 brute-force unit... And there is some poetic justice in converting an encryption device into a crypto breaker